The Windows 10 Fall Creators Update has a very useful new feature that can dramatically reduce the impact of ransomware: Controlled Folders. You should turn it on (Ed Bott’s article tells you how). Once it’s on, any attempt by an unauthorized program to modify files in controlled folders (including your OneDrive and OneDrive for Business folders and your Documents folder) will fail with an error message like this:
The problem is, sometimes you want an application to have access to those folders. No problem: you can get there by opening the Windows Defender Security Center app, clicking “Virus and threat protection”, then clicking “Virus and threat protection settings,” and then finally selecting the “Allow an app through Controlled folder access.” It’s an easy enough process.
Unfortunately, you may find that the app you added to the list isn’t the app that actually runs when you try to do something. For example, when you run GitDesktop you’ll see a message like the one above because that app is actually a bundle that includes several binaries. You might think you can just add the binaries themselves, and you should be able to, but instead I got an error saying that the path I had entered wasn’t valid. That’s probably because I (lazily) installed the GitDesktop client on my… desktop… so its binaries are tucked away in my Users directory.
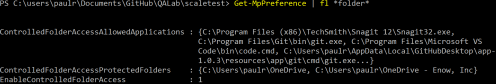
I spent some time scratching my head trying to figure out what to do, then discovered that you could enable Controlled Folder Access with the Set-MpPreference cmdlet. Of course, where there’s a Set- cmdlet, there’s usually a Get- cmdlet, and sure enough…
A little more digging turned up the Add-MpPreference cmdlet and the associated ControlledFolderAccessAllowedApplications switch. A little digging to figure out which actual copy of git.exe was being run and I was all set… until I started writing this post and found that SnagIt has the same problem!
Thus I ended up solving two problems (“why doesn’t GitDesktop work?” and “why won’t SnagIt work?”), learning something new (*-MpPreference), and, at least hopefully, protecting myself and others against ransomware. Onwards!





How is this any different from just clicking the notification and adding the application via Windows’ UI?
I’ve never seen any controls in the notification to do that– clicking the notification does nothing on my machine.
I had same problem. Some Docs are not running with my Windows10. I was surfing for finding problem about this and I saw this commend “https://forum.elysium-project.org/topic/46064-keeping-addons-up-to-date/?tab=comments#comment-429688”
But I didnt try to do that. Cuz I’m not good with coding something. Maybe you can get new ideas about your searchs. Good luck!
I had same problem. Some Docs are not running with my Windows10. I was surfing for finding problem about this and I saw this commend “https://forum.elysium-project.org/topic/46064-keeping-addons-up-to-date/?tab=comments#comment-429688”
But I didnt try to do that. Cuz I’m not good with coding something. Maybe you can get new ideas about your searchs. Good luck.